A portion of the information systems operated by a well-known logistics provider suffered a major cyberattack on July 8, 2024, resulting in service interruptions across a wide scope of operations. The incident not only caused significant disruption to logistics services, but also underscored the critical importance of robust information security protection. The information security team at CHUANG-XI Information and Technology (CXIT) closely monitored this incident and conducted an in-depth analysis.
Upon detection of the attack, the logistics provider’s information security department immediately activated defensive mechanisms and backup operations, while working in coordination with external information security specialists. Following data consolidation, the incident was reported to government law enforcement agencies and cybersecurity authorities, with ongoing coordination maintained throughout the response process.
CXIT Incident Analysis
Based on available information, the attackers may have conducted remote intrusion using a hybrid internal–external approach. The attack likely targeted sensitive data within core information systems by exploiting websites and applications. Although the exact timing of the attack could not be determined, it is suspected that the attackers used dynamic IP addresses and techniques to bypass defense mechanisms such as Web Application Firewall (WAF).
According to public disclosures, the attackers launched network-based attacks against certain information systems. These may have included Distributed Denial-of-Service (DDoS) attacks or intrusions targeting network perimeter devices such as firewalls and routers.
The detection of system anomalies indicates that monitoring mechanisms were in place and may have identified abnormal traffic patterns or unauthorized access attempts.
Following anomaly detection, the information security team activated defensive and backup procedures, which may have included isolating affected systems, activating standby servers, blocking malicious traffic, and reviewing and remediating identified vulnerabilities.
After the incident occurred, the organization promptly engaged an external information security firm, indicating that additional expert support was required to address the sophistication of the attack and to conduct deeper investigation and remediation.
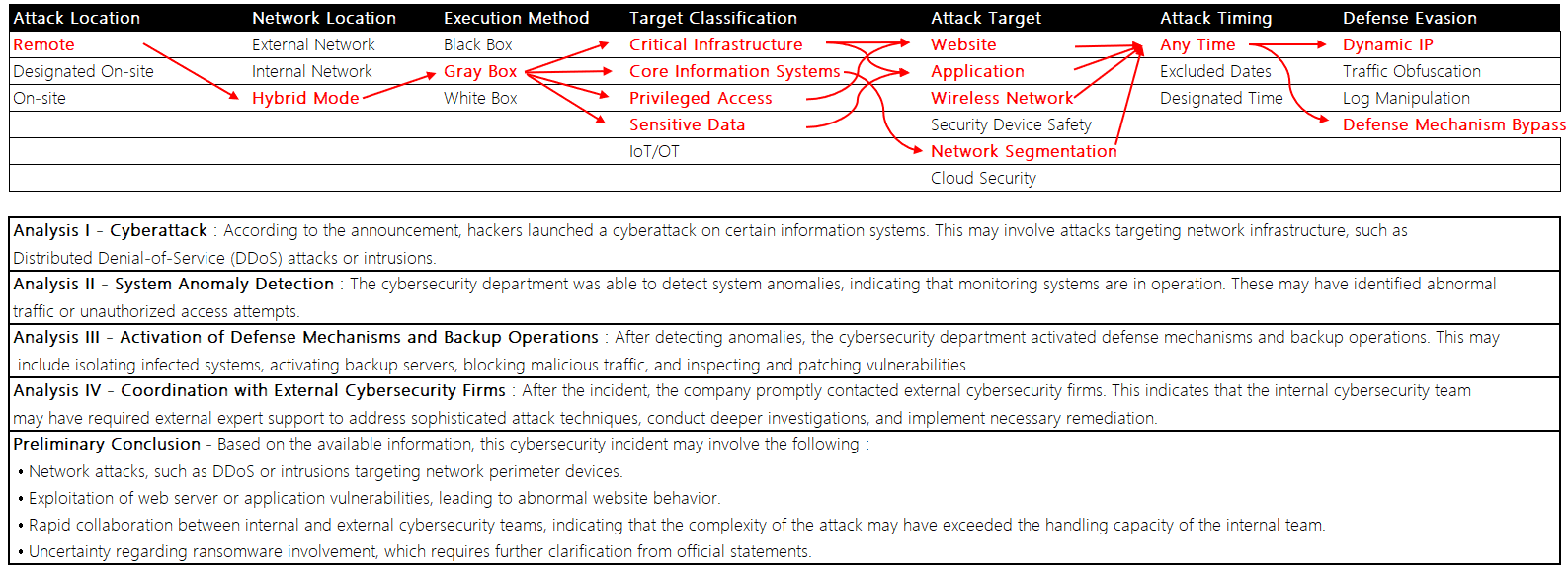
Figure 1: Intrusion Path Analysis of This Information Security Incident
Recommended Information Security Enhancements
- Intelligence Threat and Vulnerability Management
Enhance capabilities to ensure timely updates and analysis of the latest threat intelligence. - Strengthen Defensive Strategies
Implement comprehensive and detailed information security assessments. - Multi-Layered Defense Architecture
Establish a defense-in-depth strategy that emphasizes prevention rather than relying solely on post-incident detection and response.
We also recommend referencing the Cyber Defense Matrix when designing defensive strategies. The Cyber Defense Matrix is a structured framework that helps organizations understand and implement comprehensive information security controls. It consists of five security functions and five asset classes, providing a holistic view for identifying, protecting, detecting, responding to, and recovering information assets.
This incident highlights the importance of thorough threat identification (Identify) and effective multi-layered protection planning (Protect) within information security architecture, as illustrated below.
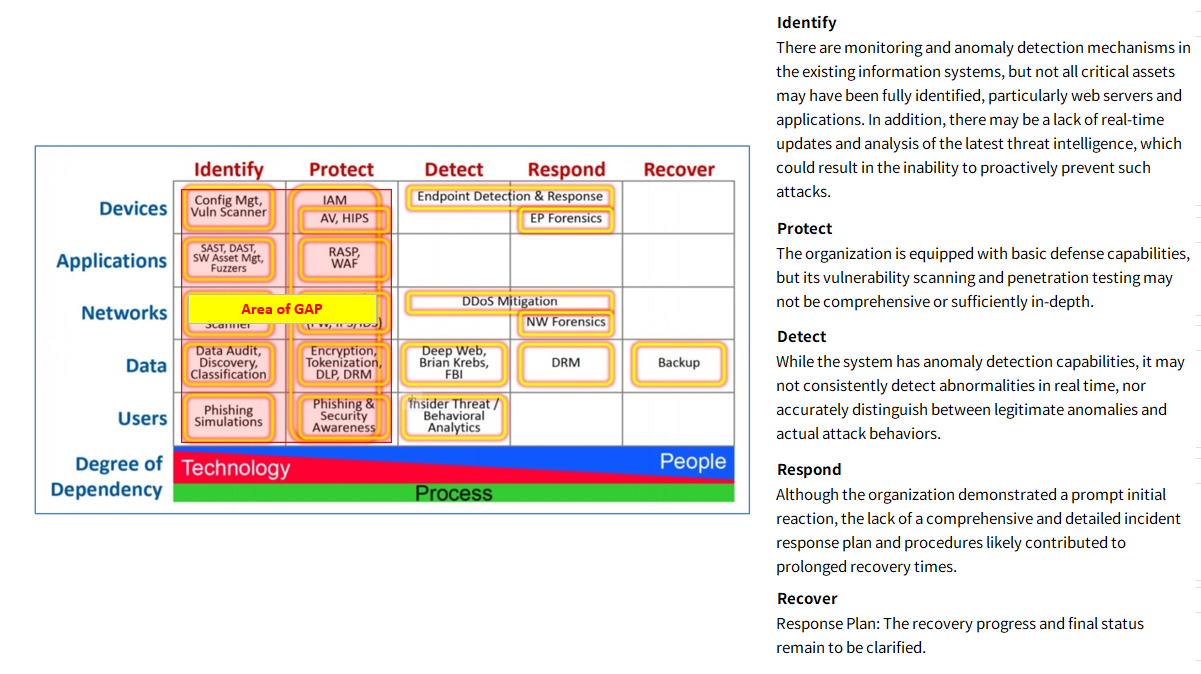
Figure 2: Cyber Defense Matrix Analysis Identifying Potential Security Gaps in This Incident
CHUANG-XI Information and Technology maintains dedicated red team and penetration testing capabilities, with team members holding internationally recognized certifications including OSCP, OSWE, OSWP, and CREST. These capabilities enable CXIT to assist clients in identifying threats to critical assets and designing appropriate protective controls.
Information security protection should prioritize prevention, rather than focusing solely on detection and response after incidents occur. CXIT also provides ISO/IEC 27001 implementation consulting services, helping organizations across industries reduce the risk of similar information security incidents.
For this incident, the following ISO/IEC 27002 controls may serve as key reference points for effective governance and mitigation:
1.A.12.6 – Technical Vulnerability Management
Identify and remediate technical vulnerabilities to reduce system and application exposure.
2.A.14.2 – Secure Testing
Conduct security testing, including penetration testing, during system development and maintenance.
3.A.15.2 – Information Security in Supplier Relationships
Ensure suppliers adhere to equivalent information security standards, including security assessments and testing.
4.A.16.1 – Information Security Incident Management
Establish and maintain incident management procedures, including simulations and red team exercises, to improve response effectiveness.
5.A.18.2 – Compliance
Ensure compliance with information security regulations and standards through regular assessment and testing.
CHUANG-XI Information and Technology possesses comprehensive information security planning and execution capabilities, enabling organizations to strengthen defenses and safeguard critical information assets. This logistics-sector incident serves as a clear reminder that prevention is the cornerstone of effective information security. CXIT remains committed to providing clients with the latest security intelligence and protective measures, working together to address future information security challenges.